Troubleshooting ISAKMP Phase 1 Messages – Part 1
This is a must-keep aide-memoir for troubleshooting VPN connections.
IKE (PHASE 1) Messages:
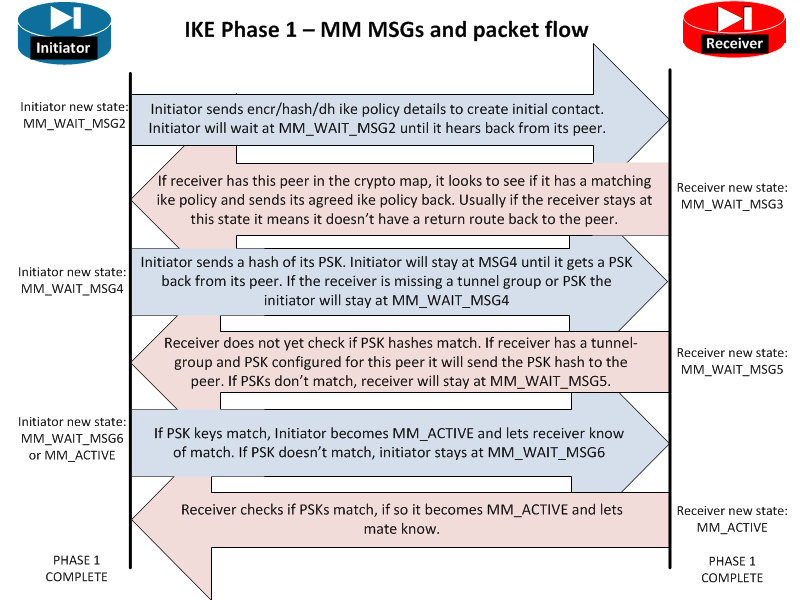
MM_WAIT_MSG2 Initiator Initial DH public key sent to responder. Awaiting initial contact reply from other side. Initiator sends encr/hash/dh ike policy details to create initial contact. Initiator will wait at MM_WAIT_MSG2 until it hears back from its peer. If stuck here it usually means the other end is not responding. This could be due to no route to the far end or the far end does not have ISAKMP enabled on the outside or the far end is down.
- MM_WAIT_MSG3 Receiver Receiver is sending back its IKE policy to the initiator. Initiator sends encr/hash/dh ike policy details to create initial contact. Initiator will wait at MM_WAIT_MSG2 until it hears back from its peer. Hang ups here may also be due to mismatch device vendors, a router with a firewall in the way, or even ASA version mismatches.
- MM_WAIT_MSG4 Initiator Initiator is sending the Pre-Shared-Key hash to its peer. Initiator sends a hash of its PSK. Initiator will stay at MSG4 until it gets a PSK back from its peer. If the receiver is missing a tunnel group or PSK the initiator will stay at MM_WAIT_MSG4
- MM_WAIT_MSG5 Receiver Receiver is sending its PSK hash to its peer. Receiver does not yet check if PSK hashes match. If receiver has a tunnel-group and PSK configured for this peer it will send the PSK hash to the peer. If PSKs don?t match, receiver will stay at MM_WAIT_MSG5. I have also seen the tunnel stop here when NAT-T was on when it needed to be turned off.
- MM_WAIT_MSG6 Initiator Initiator checks if PSK hashes match. If PSK keys match, Initiator becomes MM_ACTIVE and lets receiver know of match. If PSK doesn?t match, initiator stays at MM_WAIT_MSG6. I have also seen the tunnel stop here when NAT-T was on when it needed to be turned off. However, if the state goes to MSG6 then the ISAKMP gets reset that means phase 1 finished but phase 2 failed. Check that IPSEC settings match in phase 2 to get the tunnel to stay at MM_ACTIVE.
- AM_ACTIVE / MM_ACTIVE The ISAKMP negotiations are complete. Phase 1 has successfully completed.de exchanges.
TROUBLESHOOTING:
First enable debug of phase 1 and phase 2:
- debug crypto isakmp 128
- debug crypto ipsec 128
Use the “packet-tracer” command to generate interesting traffic (see http://darenmatthews.com/blog/?p=1944 for an explanation of what this means). Example:
packet-tracer input inside tcp 172.23.100.50 1234 123.123.123.123 80
- If you observe in the debug output, that phase 1 reaches MM_WAIT_MSG6 and stays there, the problem is likely to be a mismatch of the pre-shared key.
- If you observe in the debug output, that phase 1 reaches MM_WAIT_MSG6 and then transitions back to “no sa” that indicates that phase 1 DID complete but phase 2 is wrong.
Compare the crypto settings on each ASA. NOTE: use the “show run full” syntax as it reveals some rather important phase 2 settings. Compare the output of the two:
CiscoASA# sh run crypt | inc IPSEC-VPN
crypto ipsec transform-set IPSEC esp-3des esp-sha-hmac
crypto dynamic-map MY-IPSEC-TRANSFER-SET 65535 set transform-set ESP-AES-128-SHA ESP-3DES-SHA
crypto map MY-CRYPTO-MAP 1 match address IPSEC-VPN-INTERESTING-TRAFFIC
crypto map MY-CRYPTO-MAP 1 set pfs
crypto map MY-CRYPTO-MAP 1 set peer 213.121.63.108
crypto map MY-CRYPTO-MAP 1 set transform-set ESP-AES-128-SHA ESP-3DES-SHA
crypto map MY-CRYPTO-MAP interface outside
CiscoASA#
CiscoASA#
CiscoASA# sh run all crypt | inc IPSEC-VPN
crypto ipsec transform-set IPSEC esp-3des esp-sha-hmac
crypto dynamic-map MY-IPSEC-TRANSFER-SET 65535 set transform-set ESP-AES-128-SHA ESP-3DES-SHA
crypto map MY-CRYPTO-MAP 1 match address IPSEC-VPN-INTERESTING-TRAFFIC
crypto map MY-CRYPTO-MAP 1 set pfs group2
crypto map MY-CRYPTO-MAP 1 set connection-type bi-directional
crypto map MY-CRYPTO-MAP 1 set peer 213.121.63.108
crypto map MY-CRYPTO-MAP 1 set transform-set ESP-AES-128-SHA ESP-3DES-SHA
crypto map MY-CRYPTO-MAP 1 set inheritance rule
crypto map MY-CRYPTO-MAP 1 set phase1-mode main
crypto map MY-CRYPTO-MAP interface outside
The problem with Phase 1 completing but phase 2 not was in this case caused bytb the fact that DH Group 2 was NOT configured on the peer.
SUCCESSFUL PHASE 1 DEBUG MESSAGES:
MM_WAIT_MSG1 (connection initialised):
CiscoASA# Jan 22 10:09:26 [IKEv1 DEBUG]: Pitcher: received a key acquire message, spi 0x0
IPSEC(crypto_map_check)-3: Looking for crypto map matching 5-tuple: Prot=1, saddr=172.23.129.11, sport=7287, daddr=129.0.0.2, dport=7287
IPSEC(crypto_map_check)-3: Checking crypto map MY-CRYPTO-MAP 1: matched.
Jan 22 10:09:26 [IKEv1]: IP = 123.123.123.123, IKE Initiator: New Phase 1, Intf Inside, IKE Peer 123.123.123.123 local Proxy Address 172.23.128.0, remote Proxy Address 129.0.0.0, Crypto map (MY-CRYPTO-MAP)
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, constructing ISAKMP SA payload
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, constructing NAT-Traversal VID ver 02 payload
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, constructing NAT-Traversal VID ver 03 payload
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, constructing NAT-Traversal VID ver RFC payload
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, constructing Fragmentation VID + extended capabilities payload
MM_WAIT_MSG2 (send hash/encrypt/dh infor and agree upon them):
Jan 22 10:09:26 [IKEv1]: IP = 123.123.123.123, IKE_DECODE SENDING Message (msgid=0) with payloads : HDR + SA (1) + VENDOR (13) + VENDOR (13) + VENDOR (13) + VENDOR (13) + NONE (0) total length : 204
Jan 22 10:09:26 [IKEv1]: IP = 123.123.123.123, IKE_DECODE RECEIVED Message (msgid=0) with payloads : HDR + SA (1) + VENDOR (13) + VENDOR (13) + NONE (0) total length : 124
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, processing SA payload
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, Oakley proposal is acceptable
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, processing VID payload
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, Received NAT-Traversal RFC VID
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, processing VID payload
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, Received Fragmentation VID
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, IKE Peer included IKE fragmentation capability flags: Main Mode: True Aggressive Mode: True
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, constructing ke payload
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, constructing nonce payload
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, constructing Cisco Unity VID payload
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, constructing xauth V6 VID payload
MM_WAIT_MSG3 (find compatible vendors):
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, Send IOS VID
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, Constructing ASA spoofing IOS Vendor ID payload (version: 1.0.0, capabilities: 20000001)
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, constructing VID payload
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, Send Altiga/Cisco VPN3000/Cisco ASA GW VID
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, constructing NAT-Discovery payload
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, computing NAT Discovery hash
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, constructing NAT-Discovery payload
Jan 22 10:09:26 [IKEv1 DEBUG]: IP = 123.123.123.123, computing NAT Discovery hash
Jan 22 10:09:26 [IKEv1]: IP = 123.123.123.123, IKE_DECODE SENDING Message (msgid=0) with payloads : HDR + KE (4) + NONCE (10) + VENDOR (13) + VENDOR (13) + VENDOR (13) + VENDOR (13) + NAT-D (20) + NAT-D (20) + NONE (0) total length : 304
Jan 22 10:09:27 [IKEv1]: IP = 123.123.123.123, IKE_DECODE RECEIVED Message (msgid=0) with payloads : HDR + KE (4) + NONCE (10) + VENDOR (13) + VENDOR (13) + VENDOR (13) + VENDOR (13) + NAT-D (20) + NAT-D (20) + NONE (0) total length : 304
Jan 22 10:09:27 [IKEv1 DEBUG]: IP = 123.123.123.123, processing ke payload
Jan 22 10:09:27 [IKEv1 DEBUG]: IP = 123.123.123.123, processing ISA_KE payload
Jan 22 10:09:27 [IKEv1 DEBUG]: IP = 123.123.123.123, processing nonce payload
Jan 22 10:09:27 [IKEv1 DEBUG]: IP = 123.123.123.123, processing VID payload
Jan 22 10:09:27 [IKEv1 DEBUG]: IP = 123.123.123.123, Received Cisco Unity client VID
Jan 22 10:09:27 [IKEv1 DEBUG]: IP = 123.123.123.123, processing VID payload
Jan 22 10:09:27 [IKEv1 DEBUG]: IP = 123.123.123.123, Received xauth V6 VID
Jan 22 10:09:27 [IKEv1 DEBUG]: IP = 123.123.123.123, processing VID payload
Jan 22 10:09:27 [IKEv1 DEBUG]: IP = 123.123.123.123, Processing VPN3000/ASA spoofing IOS Vendor ID payload (version: 1.0.0, capabilities: 20000001)
Jan 22 10:09:27 [IKEv1 DEBUG]: IP = 123.123.123.123, processing VID payload
Jan 22 10:09:27 [IKEv1 DEBUG]: IP = 123.123.123.123, Received Altiga/Cisco VPN3000/Cisco ASA GW VID
Jan 22 10:09:27 [IKEv1 DEBUG]: IP = 123.123.123.123, processing NAT-Discovery payload
Jan 22 10:09:27 [IKEv1 DEBUG]: IP = 123.123.123.123, computing NAT Discovery hash
Jan 22 10:09:27 [IKEv1 DEBUG]: IP = 123.123.123.123, processing NAT-Discovery payload
Jan 22 10:09:27 [IKEv1 DEBUG]: IP = 123.123.123.123, computing NAT Discovery hash
MM_WAIT_MSG4 (Exchange PSK’s):
Jan 22 10:09:27 [IKEv1]: IP = 123.123.123.123, Connection landed on tunnel_group 123.123.123.123
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, Generating keys for Initiator…
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, constructing ID payload
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, constructing hash payload
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, Computing hash for ISAKMP
Jan 22 10:09:27 [IKEv1 DEBUG]: IP = 123.123.123.123, Constructing IOS keep alive payload: proposal=32767/32767 sec.
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, constructing dpd vid payload
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, processing ID payload
Jan 22 10:09:27 [IKEv1 DECODE]: Group = 123.123.123.123, IP = 123.123.123.123, ID_IPV4_ADDR ID received
123.123.123.123
MM_WAIT_MSG5 (check to ensure that has for both PSK’s are correct):
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, processing hash payload
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, Computing hash for ISAKMP
Jan 22 10:09:27 [IKEv1 DEBUG]: IP = 123.123.123.123, Processing IOS keep alive payload: proposal=32767/32767 sec.
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, processing VID payload
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, Received DPD VID
Jan 22 10:09:27 [IKEv1]: IP = 123.123.123.123, Connection landed on tunnel_group 123.123.123.123
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, Oakley begin quick mode
MM_WAIT_MSG6
Jan 22 10:09:27 [IKEv1 DECODE]: Group = 123.123.123.123, IP = 123.123.123.123, IKE Initiator starting QM: msg id = c4aad28b
Jan 22 10:09:27 [IKEv1]: Group = 123.123.123.123, IP = 123.123.123.123, PHASE 1 COMPLETED
Jan 22 10:09:27 [IKEv1]: IP = 123.123.123.123, Keep-alive type for this connection: DPD
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, Starting P1 rekey timer: 24480 seconds.
SUCCESSFUL PHASE 2 DEBUG MESSAGES:
IPSEC: New embryonic SA created @ 0xAFF0BF10,
SCB: 0xB00DD118,
Direction: inbound
SPI : 0xF0724F55
Session ID: 0x0007D000
VPIF num : 0x00000004
Tunnel type: l2l
Protocol : esp
Lifetime : 240 seconds
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, IKE got SPI from key engine: SPI = 0xf0724f55
IPSEC: New embryonic SA created @ 0xAFACD218,
SCB: 0xACD38528,
Direction: inbound
SPI : 0xE301C31A
Session ID: 0x0007D000
VPIF num : 0x00000004
Tunnel type: l2l
Protocol : esp
Lifetime : 240 seconds
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, IKE got SPI from key engine: SPI = 0xe301c31a
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, oakley constucting quick mode
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, constructing blank hash payload
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, constructing IPSec SA payload
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, constructing IPSec nonce payload
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, constructing pfs ke payload
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, constructing proxy ID
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, Transmitting Proxy Id:
Local subnet: 172.23.128.0 mask 255.255.252.0 Protocol 0 Port 0
Remote subnet: 129.0.0.0 Mask 255.255.0.0 Protocol 0 Port 0
Jan 22 10:09:27 [IKEv1 DECODE]: Group = 123.123.123.123, IP = 123.123.123.123, IKE Initiator sending Initial Contact
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, constructing qm hash payload
Jan 22 10:09:27 [IKEv1 DECODE]: Group = 123.123.123.123, IP = 123.123.123.123, IKE Initiator sending 1st QM pkt: msg id = c4aad28b
Jan 22 10:09:27 [IKEv1]: IP = 123.123.123.123, IKE_DECODE SENDING Message (msgid=c4aad28b) with payloads : HDR + HASH (8) + SA (1) + NONCE (10) + KE (4) + ID (5) + ID (5) + NOTIFY (11) + NONE (0) total length : 388
Jan 22 10:09:27 [IKEv1]: IP = 123.123.123.123, IKE_DECODE RECEIVED Message (msgid=c4aad28b) with payloads : HDR + HASH (8) + SA (1) + NONCE (10) + KE (4) + ID (5) + ID (5) + NONE (0) total length : 308
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, processing hash payload
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, processing SA payload
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, processing nonce payload
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, processing ke payload
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, processing ISA_KE for PFS in phase 2
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, processing ID payload
Jan 22 10:09:27 [IKEv1 DECODE]: Group = 123.123.123.123, IP = 123.123.123.123, ID_IPV4_ADDR_SUBNET ID received–172.23.128.0–255.255.252.0
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, processing ID payload
Jan 22 10:09:27 [IKEv1 DECODE]: Group = 123.123.123.123, IP = 123.123.123.123, ID_IPV4_ADDR_SUBNET ID received–129.0.0.0–255.255.0.0
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, Pitcher: received key delete msg, spi 0xe301c31a
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, loading all IPSEC SAs
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, Generating Quick Mode Key!
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, NP encrypt rule look up for crypto map DST-TROWE-CRYPTO-MAP 1 matching ACL TROWE-VPN-INTERESTING-TRAFFIC: returned cs_id=ae29fab8; rule=afe1d3b0
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, Generating Quick Mode Key!
IPSEC: New embryonic SA created @ 0xAFACD218,
SCB: 0xACD38528,
Direction: outbound
SPI : 0x0CD10E9B
Session ID: 0x0007D000
VPIF num : 0x00000004
Tunnel type: l2l
Protocol : esp
Lifetime : 240 seconds
IPSEC: Completed host OBSA update, SPI 0x0CD10E9B
IPSEC: Creating outbound VPN context, SPI 0x0CD10E9B
Flags: 0x00000005
SA : 0xAFACD218
SPI : 0x0CD10E9B
MTU : 1500 bytes
VCID : 0x00000000
Peer : 0x00000000
SCB : 0x0FE92425
Channel: 0xA7A9C280
IPSEC: Completed outbound VPN context, SPI 0x0CD10E9B
VPN handle: 0x0001BFAC
IPSEC: New outbound encrypt rule, SPI 0x0CD10E9B
Src addr: 172.23.128.0
Src mask: 255.255.252.0
Dst addr: 129.0.0.0
Dst mask: 255.255.0.0
Src ports
Upper: 0
Lower: 0
Op : ignore
Dst ports
Upper: 0
Lower: 0
Op : ignore
Protocol: 0
Use protocol: false
SPI: 0x00000000
Use SPI: false
IPSEC: Completed outbound encrypt rule, SPI 0x0CD10E9B
Rule ID: 0xACD25390
IPSEC: New outbound permit rule, SPI 0x0CD10E9B
Src addr: 192.160.242.66
Src mask: 255.255.255.255
Dst addr: 123.123.123.123
Dst mask: 255.255.255.255
Src ports
Upper: 0
Lower: 0
Op : ignore
Dst ports
Upper: 0
Lower: 0
Op : ignore
Protocol: 50
Use protocol: true
SPI: 0x0CD10E9B
Use SPI: true
IPSEC: Completed outbound permit rule, SPI 0x0CD10E9B
Rule ID: 0xACD20520
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, NP encrypt rule look up for crypto map DST-TROWE-CRYPTO-MAP 1 matching ACL TROWE-VPN-INTERESTING-TRAFFIC: returned cs_id=ae29fab8; rule=afe1d3b0
Jan 22 10:09:27 [IKEv1]: Group = 123.123.123.123, IP = 123.123.123.123, Security negotiation complete for LAN-to-LAN Group (123.123.123.123) Initiator, Inbound SPI = 0xf0724f55, Outbound SPI = 0x0cd10e9b
Jan 22 10:09:27 [IKEv1 DEBUG]: Group = 123.123.123.123, IP = 123.123.123.123, oakley constructing final quick mode
IPSEC: Completed host IBSA update, SPI 0xF0724F55
IPSEC: Creating inbound VPN context, SPI 0xF0724F55
Flags: 0x00000006
SA : 0xAFF0BF10
SPI : 0xF0724F55
MTU : 0 bytes
VCID : 0x00000000
Peer : 0x0001BFAC
SCB : 0x0FE7DCEF
Channel: 0xA7A9C280
IPSEC: Completed inbound VPN context, SPI 0xF0724F55
VPN handle: 0x0001C524
IPSEC: Updating outbound VPN context 0x0001BFAC, SPI 0x0CD10E9B
Flags: 0x00000005
SA : 0xAFACD218
SPI : 0x0CD10E9B
MTU : 1500 bytes
VCID : 0x00000000
Peer : 0x0001C524
SCB : 0x0FE92425
Channel: 0xA7A9C280
IPSEC: Completed outbound VPN context, SPI 0x0CD10E9B
VPN handle: 0x0001BFAC
IPSEC: Completed outbound inner rule, SPI 0x0CD10E9B
Rule ID: 0xACD25390
IPSEC: Completed outbound outer SPD rule, SPI 0x0CD10E9B
Rule ID: 0xACD20520
IPSEC: New inbound tunnel flow rule, SPI 0xF0724F55
Src addr: 129.0.0.0
Src mask: 255.255.0.0
Dst addr: 172.23.128.0
Dst mask: 255.255.252.0
Src ports
Upper: 0
Lower: 0
Op : ignore
Dst ports
Upper: 0
Lower: 0
Op : ignore
Protocol: 0
Use protocol: false
SPI: 0x00000000
Use SPI: false
IPSEC: Completed inbound tunnel flow rule, SPI 0xF0724F55
Rule ID: 0xAFDB3670
IPSEC: New inbound decrypt rule, SPI 0xF0724F55
Src addr: 123.123.123.123
Src mask: 255.255.255.255
Dst addr: 192.160.242.66
Dst mask: 255.255.255.255
Src ports
Upper: 0
Lower: 0
Op : ignore
Dst ports
Upper: 0
Lower: 0
Op : ignore
Protocol: 50
Use protocol: true
SPI: 0xF0724F55
Use SPI: true
IPSEC: Completed inbound decrypt rule, SPI 0xF0724F55
Rule ID: 0xACCF7240
IPSEC: New inbound permit rule, SPI 0xF0724F55
Src addr: 123.123.123.123
Src mask: 255.255.255.255
Dst addr: 192.160.242.66
Dst mask: 255.255.255.255
Src ports
Upper: 0
Lower: 0
Op : ignore
Dst ports
Upper: 0
Lower: 0
Op : ignore
Protocol: 50
Use protocol: true
SPI: 0xF0724F55
Use SPI: true
IPSEC: Completed inbound permit rule, SPI 0xF0724F55
Rule ID: 0xAFD157E8
messages and diagram reproduced from tunnelsup.com